1 Introduction: Colonial Payment Infrastructure
Historically, payment, especially if it was to reach across geographical boundaries and long distances, was complex, cumbersome, and materially heavy. Consider the British practice of countermarking coin at the time of its appropriation and exploitation of the Caribbean during the seventeenth and eighteenth centuries. A tool of British imperial rule was the imposition of currency to facilitate local economies and enable (inter-)national trade in plantation economy goods. Issuing new coins was costly and complex, which spurred the practice of ‘countermarking coins’. With small incisions, stamps, or clippings in existing coinage – for instance, coins previously issued by the Spanish Crown – the bullion was authorized for payment in imperial Britain. For example, coinage originally from Peru was countermarked for use in Jamaica or Tobago by the British colonizers with stamps superimposed on the original coinage seals and with clippings to bring the coin in line with British weights and valuation practices (Parsons, Reference Parsons2023). As such, the metal helped facilitate the transatlantic triangular trade, whereby enslaved people were shipped and put to work on Caribbean plantations, while plantation goods like sugar were shipped to Europe. At the same time, the countermarked coin signifies the reach and authority of British imperial power, whereby bullion backed by London’s Bank of England and imperial weights and valuations upheld and expanded the imperial economy – at great human cost.
In 2022, the Bank of England Museum placed on display the material examples of the countermarked coin in its ‘Slavery and the Bank’ exhibition (see Figures 8.1 and 8.2). This display emphasized the imperial authority behind the countermarked coin, with the Bank of England and the British East India Companies as the centres of authority enabling the circulation of coin from, for example, Peru to Jamaica, St Lucia, and Tobago. As curator Kirsty Parsons concludes: ‘These coins help reveal the relationship between transatlantic slavery, colonialism, and the British economy’ (Parsons, Reference Parsons2023). The countermarked coin both inscribed and was inscribed by British imperial authority. As such, this payment infrastructure encodes particular hierarchies of power and cross-border territorial authority with extensive geographical reach. Those power structures may endure sedimented inside the material form, even when the power of the underlying authorities is challenged, as was the case for the Spaniards in this example.

Figure 8.1 St Lucia coin.
Countermarked coin for use in St Lucia, about 1813.
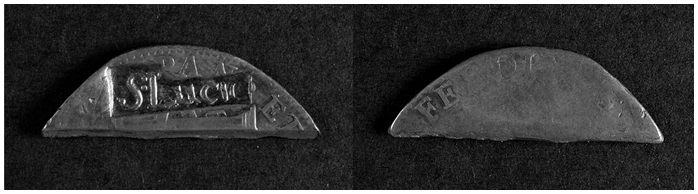
Figure 8.2 Martinique coin.
Countermarked coin for use in Martinique, about 1719.
In this chapter, we theorize payment infrastructures as crucial material sites of hegemonic power. The account of the countermarked coin illustrates three points that are at the heart of this chapter. First, the material form of payment technologies and the unequal routes of circulation produced by them are integral parts of the ways in which modern money and finance exercise power. Payment technology is not a neutral infrastructure, but a carrier of hegemonic power and a potential site of hegemonic contestation. The material remarking of bullion whereby the British Empire literally stamped over the insignia of the Spanish Crown shows how this payment technology is profoundly political and a site of power. Secondly, payment infrastructure is inextricably connected to state security and sovereignty. The countermarked coin both was enabled by the authority of the British Crown and helped further circulate the British Empire’s authority and economic power. State security and sovereignty were enabled and made durable with and through the payment infrastructure. Thirdly, infrastructures are historically durable, though they may be rerouted or reinscribed. As Susan Leigh Star has put it: ‘Infrastructure does not grow de novo. It wrestles with the inertia of the installed base and inherits strengths and limitations from that base’ (1999, p. 382). New uses or purposes can be grafted onto existing material technologies, reorienting them to new practices of power. In our example, the power of Spanish imperialism remains sedimented inside the repurposed coin, even if it was overridden and reoriented through British rule.
This chapter analyses how hegemony is embodied within payment infrastructures, thus linking political power to social-political materialities. As this edited volume shows, global financial architecture builds on human and non-human infrastructures, including institutions, currencies, and payment routes that determine global flows of liquidity and money. While semantically close, we seek to distinguish our approach from the notion of infrastructural power developed by Michael Mann (Reference Mann1984). As Coombs (Chapter 4) discusses, Mann employs ‘infrastructure’ loosely, and it is unclear whether his understanding significantly differs from that of a network. There is no well-defined distinction between the agency of organizations/networks and the background work of infrastructure in Mann’s work.
In contrast, we propose that infrastructures themselves are important material actors and sites of agentic capacity. Keller Easterling (Reference Easterling2014, p. 15) emphasizes in her study of statecraft why we need to pay attention to the capacities encoded in infrastructures themselves:
Contemporary infrastructure … orchestrates activities that can remain unstated but are nevertheless consequential. Some of the most radical changes to the globalizing world are being written, not in the language of law and diplomacy, but in these spatial, infrastructural technologies – often because market promotions or prevailing political ideologies lubricate their movement through the world.
Building on the work of Easterling and others, we propose the notion of ‘hegemony as infrastructure’ (de Goede and Westermeier, Reference Westermeier2022, p. 4). This notion helps shift focus towards the technical specifications, economic motivations, and physical pathways embedded within infrastructures and then unpack how they inherently involve complex political dynamics. In this perspective, infrastructures are not mere instruments for facilitating hegemonic power, but are conceptualized as both obstacles and arenas where hegemonic power is not only exercised but also influenced, impeded, and directed in distinct manners.
Drawing on existing literature that has focused on non-financial types of infrastructure, including railways and waterworks (Star, Reference Star1999; Mukerji, Reference Mukerji2010; Lancione and McFarlane, Reference Lancione, McFarlane, Blok and Farias2016), we distil three elements that typify the hegemonic power of infrastructure and that can be used when taking ‘infrastructure’ as the starting point for analysis. These elements are: (1) sedimentation; (2) reach; and (3) disposition. First, the notion of sedimentation helps unpack the temporalities ‘frozen’ inside infrastructural technologies and routes (Folkers, Reference Folkers2017; de Goede and Westermeier, Reference Westermeier2022). This refers to both past power hierarchies that have become sedimented in the technology and future orientations that are thus made possible. Secondly, the notion of reach helps unpack the ways in which geographical space is (dis)connected through infrastructures – as with the example of the clipped coin. Thirdly, the term disposition refers to the particular choices, directions, and (im)possibilities encoded into infrastructure. This is the concept that Easterling (Reference Easterling2014, p. 21) uses to theorize ‘the unfolding potentials or inherent agency’ in a material structure like a river, a piece of fabric, or a game piece. The disposition of an infrastructure is the agency encoded into its material and technological propensities.
We develop the notion of infrastructure as hegemony further in Section 2. Then we illustrate the arguments empirically by referring to the so-called financial war on terror, where financial infrastructures became a major but highly depoliticized site of security power. Empirically, this chapter focuses on a contemporary parallel to the countermarked coin: the way in which the payment technology SWIFT (Society for Worldwide Interbank Financial Telecommunication) is being appropriated for security purposes. Since the terrorist attacks in the United States that occurred on 11 September 2001 (the events now known as 9/11), the financial payment infrastructure SWIFT has become a site of political contestation and hegemonic struggle. This contestation has (re)made visible how the aims and routes of the (post-Bretton Woods) liberal world order have been encoded into the seemingly technical communications infrastructure of SWIFT. By adopting the lens of infrastructure-as-hegemony, it becomes evident that infrastructures hold significance beyond being mere tools. They possess the capacity to shape the trajectory of hegemonic power through their intrinsic attributes and interactions. Rather than solely serving as vehicles for the exertion of hegemonic influence, infrastructures can also become stumbling blocks that challenge or redirect political practice. Infrastructural configurations essentially are pivotal points where political forces converge, diverge, and evolve, contributing to the shaping of hegemonic power in diverse and intricate ways.
2 Finance/Security Infrastructure
Financial infrastructure acts as a site of hegemonic expansion, consolidation, strengthening, and contestation. This chapter’s point of departure is that financial infrastructures are not simply (‘neutral’) lifelines of international trade, directing the flow of funds and enabling access to them. They also produce and enhance global (inter-)dependencies via interconnectivities and disconnections, and transform international security and the international political economy through new (economic) technologies.
Yet, the concrete infrastructures that enable the currency to be transferred and monitor its usage have received relatively little attention in analyses of financial and political hegemonies (but see, e.g., Maurer, Reference Maurer2015; Lauer, Reference Lauer2020). Questions of power in finance are often discussed in terms of quantities of financial flows and the dominance of certain currencies that are reflected in the quantities of their usage. The history of payment itself is often analysed in terms of increasing speed, diminishing weight, and extending reach. Research in the social studies of finance and international political economy has focused on the increasing abstraction, fictitiousness, and ephemerality of money and financial transactions (Martin, Reference Martin2007; LiPuma and Lee, 2015; O’Dwyer, Reference O’Dwyer2019). Contemporary card and mobile payment technologies are indeed a far cry from the heft of early modern bullion and from the complexity and fallibility of clipping and countermarking coin.
However important the narrative of the power of ‘frictionless finance’, it risks underplaying the material complexity and geographical unevenness of finance and payment infrastructures and how these have historically evolved. This chapter understands infrastructure as socio-technical relations and more concretely as ‘an articulation of materialities with institutional actors, legal regimes, policies, and knowledge practices that is constantly in formation across space and time’ (Anand, Gupta, and Appel, Reference Anand, Appel, Gupta, Anand, Gupta and Appel2018, p. 12; see Chapter 1 in this volume). This perspective views infrastructure as inherently both material and socio-political, serving as a gateway to understanding the political economy of technology. Infrastructure is more than matter; it encompasses not only physical substance but also extends beyond matter to include scientific observations, plans, and apparent intangibles, such as political imagination and future planning. Therefore, any examination of the materiality of infrastructure must address both the foundational and evolving composition of infrastructure and the ostensibly immaterial aspects (Barry, Reference Barry, Maasen, Dickel and Schneider2020, p. 93). As argued by Anand, Gupta, and Appel, drawing on Edwards et al. (Reference Edwards, Bowker, Jackson and William2009, p. 12), infrastructures possess ‘histories and “grow” incrementally in a dynamic temporal, spatial, and political environment […]. They are formed with the moralities and materials of the time and political moment in which they are situated.’
As the coin countermarking example shows, moreover, financial infrastructures have long been a focal point of states’ and empires’ security strategies. Notions and understanding of security change over time, ranging from traditional military security to cold war and nuclear security, to widened notions of cyber and public health security. Infrastructures play a central role for security practitioners, as they enable the fixation and control of the flow of vital goods and people. This was starkly illustrated during the COVID pandemic that took off in 2020, when movements of people were interrupted and stopped by limiting access to infrastructures of mobility. At the same time, financial infrastructure served to keep economic processes of production, distribution, and consumption going (Langenohl and Westermeier, Reference Langenohl and Westermeier2021). Security politics not only uses the steering capacity of infrastructures, but the politics of security is built into them. Critical security studies have drawn attention to security infrastructures, such as CCTV (closed circuit television), algorithms, scoring and ranking practices, and the securitization of infrastructures, often via the notion of critical infrastructure (Aradau, Reference Aradau2010; Langenohl, Reference Langenohl2020). Recent analysis also points to the concept of ‘infrastructural insecurity’ as a deliberate strategy to render (telecommunications) infrastructure susceptible to becoming ‘a venue for geopolitical interests’ (Ten Oever and Becker, Reference Ten Oever and Becker2024, p. 1).
With regard to financial infrastructures, the term ‘finance/security infrastructure’ foregrounds the intrinsic relations of the two notions and draws analytical attention to payment infrastructure and its political, technical, and colonial histories (de Goede, Reference de Goede2020). The term also emphasizes the ways in which financial infrastructure and state security practices are historically interlinked. The post-9/11 ‘war’ on terrorism financing provides a crucial current example that will be explored in the remainder of this chapter. Anti-terrorism financing measures seek to direct and reroute financial flows and to make them traceable (Westermeier, Reference Westermeier2022). These financial security measures are simply not feasible without financial infrastructures as modes of control that include a variety of diverse elements, such as banks and financial networks, security practitioners, risk registers and sanctions lists, to name only a few (Amicelle and Jacobsen, Reference Amicelle and Jacobsen2016). Sanctions, currently among the most prevalent security measures, are inconceivable without infrastructural control. Infrastructural reach enables and limits the imposition of sanctions, as discussed later in this chapter. Although financial transactions have transitioned to digital formats and circulate as data, they still rely on concrete channels and platforms. Money does not simply ‘flow’ from one account to another; it is actively directed and accounted for. Particularly, international transactions pass through several infrastructural actors and institutions (Robinson, Dörry, and Derudder, this volume).
The remainder of this chapter discusses the three elements of sedimentation, reach, and disposition as tools to track how political hegemonies endure in financial infrastructures and become challenged. Our approach puts a focus on past and present notions of security politics and how these are built into financial infrastructures.
3 Temporalities of Infrastructure: Sedimentation
There is a long tradition in the social sciences that has emphasized the temporal politics of infrastructure (Star, Reference Star1999; Mukerji, Reference Mukerji2010). Studies on dams, roads, railways, and waterways, for example, have foregrounded how these are intrinsically linked to notions of modernity and their role in furthering modern states’ political ambitions (see Langenohl’s chapter, this volume). Far from technological determinism, studies into the politics of technology show how technology is inherently political. In developing and adopting certain technologies, political actors opt for more than appears at first sight. Technologies enable or disable certain options, and some are more aligned with certain political actions than others, although they do not necessarily require or determine them. In other words, not only can the design features of a technology be political, but the technology is political (see also MacKenzie and Wajcman, 1999; Easterling, Reference Easterling2014). Following this line of research, infrastructure is fundamentally both material and political, forming a point of entry into the political economy of technology.
The first element that the study of infrastructures brings into view is that of temporality: infrastructure is about ‘the long-term rhythms of the community’ (Star Reference Star1999, p. 381). Infrastructure connects the past with the present and gestures towards anticipated futures. Infrastructures sediment past power relations, making them viable in the present even though the political regime that established them may seem far gone. Infrastructures are linked to political rationalities: the material structure of infrastructure makes them somewhat resistant to sudden change and constrains political ambitions that run counter to how the infrastructure is set up (Collier, Reference Collier2008; Opitz and Tellmann, Reference Opitz and Tellmann2015). While digital infrastructures may seem readily adaptable to change, underlying protocols and standards set limits to the updates of platforms and applications. Recent contributions to the field of financial subordination have foregrounded the violent practices that are built into financial infrastructure which still endure today (de Goede, Reference de Goede2020; Alami et al., Reference Alami, Alves, Bonizzi, Kaltenbrunner, Koddenbrock, Kvangraven and Powell2022). The introductory example of the colonial coins provides a striking image of how colonial legacies are forced onto the colonized (Koddenbrock, Reference Koddenbrock2020).
Thinking about infrastructures as sedimented hegemony allows a perspective that brings to the fore the political character of these material connections that is often forgotten when they are described as background or invisible. Infrastructures are materializations of hegemonic projects, such as globalization or mobility, that are present and largely consensual at a specific time and place. As infrastructure endures over years and decades, the hegemonies that were present at the time of fixation pertain to a certain moment in time as well as to this moment’s vision of the future: if the hegemonic order changes, if common wisdom alters, the infrastructure and its rooting may itself become a matter of contestation again. Still, contestation does not necessarily entail change within the infrastructure in question, but might instead take alternative courses, as we will discuss in the following.
In the example of the financial war on terror after 9/11, it became starkly visible that payment infrastructure entails sedimented rationalities and hegemonic order. Everyday international payment transactions are rendered possible through SWIFT, a relatively invisible global network set up in the 1970s to facilitate global trade. As part of the post-9/11 security regime, the United States Treasury, in collaboration with the Central Intelligence Agency (CIA), successfully obtained access to SWIFT data under the auspices of the Terrorist Finance Tracking Program in October 2001 (de Goede, Reference de Goede2012b). This initiative formed an integral component of the broader post-9/11 shift towards a risk-based utilization of commercial data for security objectives, emanating from the George W. Bush administration’s aspiration to harness technological tools for the prevention of future terrorist incidents (de Goede Reference de Goede2012a). The analysis of SWIFT data was directed towards the identification of financial transactions, interconnections, and networks associated not only with the 9/11 perpetrators but also encompassing investigations into other suspected terrorists and designated entities (Amicelle, Reference Amicelle2011). SWIFT has now become, as one observer calls it, ‘a centerpiece of the West’s economic arsenal’, because it has not only delivered transactions data to the CIA in the continuing combat against terrorism financing but also disconnected Iran from its global services (Lipsky and Kumar, Reference Lipsky and Kumar2023). Discussions on the potential disconnection of Russia from the SWIFT infrastructures surged after the Ukraine invasion in February 2022.
This ‘weaponization’ of SWIFT is more than the political abuse of an otherwise neutral payment technology. On the contrary, it shows that SWIFT was a political technology from the beginning, offering particular routes and connecting some places better than others. SWIFT emerged in the post-Bretton Woods financial world order to facilitate frictionless global finance and thus encodes the hegemonic ambitions of the time (Scott and Zachariadis, Reference Scott and Zachariadis2014). Yet SWIFT’s connectivity was always partial and incomplete, as, for example, former colonies are still often connected through their past colonial capitals. As Leigh Star has pointed out, infrastructure’s politics are rendered visible through the ‘situations of those who are not served by a particular infrastructure’ (1999, p. 380).
In the same vein, as past infrastructures continue to have an effect in the present, current infrastructural planning, especially public infrastructure projects, entails a certain vision of the future. For example, the ways in which contemporary infrastructures are designed make certain means of circulation more likely than others. As the chapters on digital financial infrastructures (Part III of this volume) show, they embody the cultural, political, and societal conceptions that are dominant at the time of their planning and creation, and they also carry specific notions about anticipated future developments. Collier (Reference Collier2008) emphasizes the possible failure of ‘programming’ and reprogramming – a political attempt to use existing socio-technical and political formations for a new political agenda. Notably, several digital financial technologies are designed as ways to reshape the existing financial architecture (see chapters by Ehlke and Salzer, this volume). While some financial technologies, especially in Europe, build on existing financial infrastructures to enhance financial activities (Westermeier, Reference Westermeier2020), many non-Western countries tend to leapfrog these interactions between old and new financial infrastructures. In many cases, political change entails infrastructural visioning that seeks to challenge old and enhance emerging hegemonies.
4 Infrastructural Reach
The second element that a focus on infrastructure brings into view is that of spatiality. The term ‘infrastructure’ originated in 1875, coinciding with the period when European states aspired to extend logistical control beyond their national territories and over their overseas colonial ‘possessions’ (Schouten and Bachmann, Reference Schouten and Bachmann2022; referring to Mitchell, Reference Mitchell2014; Carse, Reference Carse, Harvey, Jensen and Morita2016). However, this was rarely meant to create equal relationships between colonized and colonizing societies, as Langenohl’s chapter discusses (this volume). John Allen (Reference Allen2016, pp. 36–37) uses the concept of ‘reach’ to analyse the ways in which space is ‘folded and stretched’ to produce ‘proximity, presence and distance’. Such presence and proximity cannot fully be captured with traditional measures of distance, thus reach is about the ways in which ‘powerful actors make their presence felt’ (Allen, Reference Allen2016, p. 11). While infrastructures are often described as enabling the governance of a (state’s) territory, a focus on reach shows how infrastructural power extends well beyond its borders and may be experienced as very proximate in everyday life, for example, through the circulation of coin with stamped authority figures. At the same time, vast areas within a country might also escape the reach of state infrastructure – for example, poorer and neglected areas that are badly connected to public transport or public services (Nolte, Reference Nolte2016). This can be due to formidable engineering challenges or because such endeavours are deemed excessively expensive for states to include in their infrastructure networks. Furthermore, states may intentionally avoid constructing infrastructure in designated frontier regions to avoid integrating specific populations (Schouten and Bachmann, Reference Schouten and Bachmann2022).
Thus, infrastructures, especially financial infrastructures, entail uneven geographies that are best conceptualized through the notion of reach, which draws attention to exclusions and divisions. This is also the case with SWIFT, which is itself is a product of the expansion of international financial trade and globalization in a particular historical era. From the outset, European and US banks propelled the network, transforming it into an essential hub of the international payment system (Robinson, Dörry, and Derudder, this volume). The above mentioned mobilization of SWIFT for security purposes began after the 9/11 terrorist attacks on major US landmarks, including the World Trade Center, in 2001. As part of the ‘war against terror’, the USA secured access to transaction data transmitted through the SWIFT system. This practice came to public attention only in 2006 when it was revealed that European bank data was also being shared with US intelligence agencies in a complex arrangement whereby SWIFT had agreed to share data from its US-based server with the US Treasury and the CIA. In this manner, the SWIFT infrastructure made it possible for US security services to extend their reach by giving them access to global financial transactions data that would otherwise have had to be subpoenaed in complex juridical procedures. European countries were taken aback, not least because SWIFT, headquartered in Brussels, is subject to European Union law. That SWIFT affair points to how finance and security are imbedded in infrastructures aiming to collect, surveil, and control transactional data, going beyond the territoriality of a specific country.
The concept of infrastructural reach thus enables us to capture how certain actors expand political reach via infrastructures. As the example of SWIFT and the post-9/11 activity shows, the United States leverage their dominant position within the financial system to expand their reach within financial infrastructures although these infrastructures do not fall under their jurisdiction and are not physically based on their territory. The infrastructural reach of the United States thus rests on several pillars that often reflect past power relations that persist in infrastructures and are thus still effective today. As the central actor in the post-Bretton Woods financial order, the United States gained a pivotal role in the international financial architecture. The dominance of Western financial politics, integrated with post-colonial dynamics, has solidified within the SWIFT infrastructure, consequently positioning the company as an indispensable gateway (Dörry, Robinson, and Derudder, Reference Dörry, Robinson and Derudder2018; de Goede, Reference de Goede2020). These effects are still felt today, as several countries in Africa and South America remain poorly connected to the network. Banks also report problems with transactions between African countries and China due to differing alphabetical and numerical systems.
Along with SWIFT, the infrastructural reach of the United States is extended via so-called correspondent banks. The decline in the number of correspondent banks by 22% between 2011 and 2020 has given US-based correspondent banks renewed importance (Nance and Tsingou, this volume). Their role is closely linked to the role of the US dollar as the international reserve currency. The majority of international trade is conducted using the reserve currency, controlled by the US Federal Reserve. In the past, the USA has made the claim that all transactions in US dollars fall under US jurisdiction, thus expanding their infrastructural reach via the currency that circulates. Correspondent banks process international payments for other banks, thus serving as further nodes for payment flows. With their decline in numbers, the remaining correspondent banks have become pivotal for security politics, such as sanctions. In February 2022, the Russian Sberbank had its role as a correspondent bank with the US financial system revoked in the context of US sanctions against Russia following its invasion of Ukraine. Sberbank is the largest state-owned Russian bank, holding nearly a third of all Russian bank deposits. As a consequence of the infrastructural disconnection, it is unable to trade using US dollars.
5 Disposition of Payment Infrastructure
Within infrastructures, past political choices are materially sedimented and enable an infrastructural reach which might go beyond a specific territory. The third element in our approach comprises the ways in which past choices materialize in so-called dispositions, which at the same time enable or constrain material possibilities (Easterling, Reference Easterling2014). ‘Disposition’ helps to capture how sedimented politics shape the active form of infrastructure and thus facilitate or limit (political) agency. Keller Easterling (Reference Easterling2014, p. 73) theorizes disposition as a ‘stubborn [form] of power …hiding in the folds’. Further:
Disposition […] is the medium, not the message. It is not the pattern printed on the fabric but the way the fabric floats. It is not the shape of the game piece but the way the game piece plays … Not the object form, but the active form.
Thus, disposition refers to the sedimented politics and material propensities of an infrastructural arrangement.
What is the disposition of a financial infrastructure in the examples discussed in this chapter? Surely, there are several dispositions in each example that work to enable and disable certain flows of information, money, or other financial assets. With regard to the example of the colonial coin, we can say that its disposition entailed the way in which the Crown’s insignia circulated through it. The coin was authorized by the British Crown as visible through the stamps and clippings depicted at the beginning of this chapter. But the coin also helped fortify the Crown’s authority through its circulation. Thus, the material form of colonial coin helped strengthen the Crown’s authority; it was disposed towards the British Crown.
With regard to the contemporary nexus of financial infrastructure and security, a key disposition of SWIFT’s digital infrastructures is the traceability of money and financial transactions. This traceability is now regarded as a crucial avenue to detect illicit financial flows and halt unwanted financial transactions. Traceability is enabled by the active form of payment infrastructure: their way of storing and enabling transactions enables the traceability of money (Westermeier, Reference Westermeier2022). Money relies on infrastructures to preserve attributes like ownership, which are not inherently contained within the amount of money transferred. Money – meaning the amount of a certain currency – does not provide information about its origins and destination; it is notoriously fungible and anonymous. Yet information is attributed by the systems of money transfer and transaction. Confirming one’s identity is thus closely linked to the attribution of ownership of money. As banks are required to ‘know their costumers’, financial technologies often seek to link to databases that store identity information (see Jafri, this volume). These infrastructural technologies are redeployed for social policy and security practices.
The disposition of digital payment infrastructure entails the traceability of transactions. Monetary movements leave data traces when they travel from one financial node, such as banks or payment service providers, to another. This crucially includes cryptocurrencies that often generate the value of a coin as the result of their transaction history. These imprints left by money in its ‘flows’ are not generated by the money, but by the infrastructures that enable its circulation, such as bank accounts or credit card networks. When money is stored in digitized data repositories – a scenario applicable to the majority of non-cash funds – it takes on qualities akin to other digital data types. Hence, the manner in which money is in circulation, whether as physical currency, through credit card transactions, or in digital currency form, holds significance. Each of these tangible bases conveys distinct varieties of information which may potentially be shared with payment processors and other financial entities when a transaction is routed through their services. Only cash leaves no data trace. The prominent call to ‘follow the money’ essentially means to follow the traces that money leaves when it moves infrastructurally.
The disposition of traceability enables the current regime of anti-money laundering (AML) and counter-terrorism financing (CTF) regulation which was significantly shaped by the USA in its ‘war on terror’. While AML regulation had already been implemented before, the post-9/11 security regime follows the assumption that money trails reveal activities outside the financial realm. Financial events like payments, transactions, and withdrawals generate identifiable traces, implying that specific actions are recorded as data, such as time markers for payments or codes that indicate the initiator or recipient of a transaction, as well as the payment method employed (such as a credit card or a payment app). The data from financial transactions harbours substantial potential for inferring details about an individual’s undertakings, acquisitions, geographical movements, and even personal characteristics like sexual orientation and health condition, as well as religious and political inclinations (Ferrari, Reference Ferrari2020). The efficacy of financial surveillance is perceived to be maximized when the actions of targeted individuals are comprehensively documented within financial records, encompassing events that might otherwise be considered outside the financial domain. The shared belief that ‘money trails don’t lie’ has enabled a considerable regime of financial surveillance that provides the material basis for court cases on terrorism financing and other illicit behaviour (Anwar, Reference Anwar2022).
Infrastructural dispositions of payments also encompass electronic and increasingly automated systems that monitor financial flows, such as AML and CTF software (Bosma, Reference Bosma2022). The categorizations and risk assessments for these technologies are based on international regulatory standards. Within their infrastructural reach, the USA played a prominent role in establishing AML as a policy priority in international finance and in establishing the international standard setter, the Financial Action Task Force, which has implemented a coercive blacklisting strategy with little opposition from other ‘rich countries’ (Sharman, Reference Sharman2008). Instead, most of those countries supported these moves and shared a certain consensus that AML and CTF measures would increase financial security, largely overlooking or ignoring the exclusionary effects (see chapter by Nance and Tsingou on de-risking, this volume).
6 Conclusion
This chapter has foregrounded the critical role of payment infrastructures as significant sites of hegemonic power. Payment technologies – ranging from coins to bullions, electronic networks, and digital currencies – are imbued with hegemonic power relations. As infrastructures have historically enabled and sustained state power, payment infrastructures are crucially connected to practices of security and sovereignty. The chapter introduces three elements – sedimentation, reach, and disposition – to typify the hegemonic power of infrastructure, providing a framework for analysing infrastructural dynamics. Through empirical analysis centred on the financial war on terror, particularly the role of SWIFT and the traceability of money, the chapter illustrates how financial infrastructures have become central sites of security.


